Introduction to Cyber Attacks
About this Course
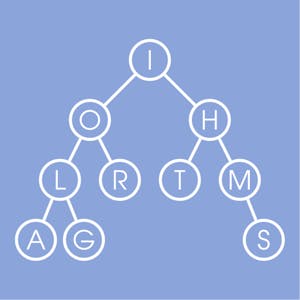
This course provides learners with a baseline understanding of common cyber security threats, vulnerabilities, and risks. An overview of how basic cyber attacks are constructed and applied to real systems is also included. Examples include simple Unix kernel hacks, Internet worms, and Trojan horses in software utilities. Network attacks such as distributed denial of service (DDOS) and botnet- attacks are also described and illustrated using real examples from the past couple of decades. Familiar analytic models are outlined such as the confidentiality/integrity/availability (CIA) security threat framework, and examples are used to illustrate how these different types of threats can degrade real assets. The course also includes an introduction to basic cyber security risk analysis, with an overview of how threat-asset matrices can be used to prioritize risk decisions. Threats, vulnerabilities, and attacks are examined and mapped in the context of system security engineering methodologies.Created by: New York University

Related Online Courses
This online course covers basic algorithmic techniques and ideas for computational problems arising frequently in practical applications: sorting and searching, divide and conquer, greedy... more
Learners in this course will examine global trade agreements -- including policies, barriers, and regulations -- of agricultural commodities, and discuss implications of world and economic... more
This course is for professionals who have heard the buzz around machine learning and want to apply machine learning to data analysis and automation. Whether finance, medicine, engineering, business... more
This course offers a comprehensive journey through the world of databases and their management on the AWS cloud platform. From understanding the core concepts of databases to mastering advanced... more
This course prepares non-native English speakers to take the reading and listening sections of the TOEFL iBT exam. It takes a close look at every type of listening and reading question that you may... more