Network and Communications Security
About this Course
Course 5: Network and Communications Security Welcome to course five: network and communication security. As we know, the explosive growth in networks, connectivity, and communications has paved the way for unprecedented transformation of business, personal, and government services into electronic, web enabled forms. This growth in e-business and e-commerce greatly expanded the threat surface. Fraudsters, criminals, unscrupulous business competitors, nation states, and non-nation state actors can take harmful actions against others worldwide. For decades, the world has operated on what is basically a network monoculture. One set of protocols and standards are used to power most of the internet, the worldwide, web e-commerce, and e-business. These standards include the open systems interconnection seven layer model from international organization for standardization and transmission. And the control protocol over internet protocol model from internet engineering taskforce. Almost every laptop, many smart devices, and other such end points use these standards to communicate with servers, and applications, and businesses, and governments. Therefore these models, or protocol stacks become our map of the threat surface. Security professionals need to have a solid understanding of modern networks and internet work concepts, techniques, technologies, and security issues. Their work is like police patrols, because they need to be familiar with the neighborhood\'s environment. Security professionals need to know the best ways to keep the neighborhood secure and to defend against attacks. The need for such a policing mentality is particularly urgent if the company has limited or no remote visibility into its operational technology systems. For this course, in module one, we start with a brief orientation to the network neighborhood, through the open systems interconnection seven layer, and transmission control protocol over internet protocol models. Then, we dive into all eight layers of this combined protocol stack. Introducing the key technologies at each layer and their regular use. In module two, we look at the various protocols that run on top of this architecture. In module three, we focus on attack and defensive strategies and tactics and build on the industry leading approach to put threat surface analysis into both the attackers and defenders operational context. In the last module, we bring these ideas together into a network security management and monitoring perspective. Now, let\'s discuss these four modules in detail. Course 5 Learning Objectives After completing this course, the participant will be able to: L5.1 - Recognize layers of the OSI model, their functions and attacks present at each layer. L5.2 - Identify commonly used ports and protocols. L5.3 - Select appropriate countermeasures for various network attacks. L5.4 - Summarize best practices for establishing a secure networked environment. Course Agenda Module 1: Apply the Fundamental Concepts of Networking (Domain 6 - Network and Communications Security) Module 2: Securing Ports and Protocols (Domain 6 - Network and Communications Security) Module 3: Network Attacks and Countermeasures (Domain 6 - Network and Communications Security) Module 4: Manage Network Security (Domain 6 - Network and Communications Security) Who Should Take This Course: Beginners Experience Required: No prior experience requiredCreated by: ISC2

Related Online Courses
This course series is designed for mid-to-senior-level professionals, including managers, business leaders, product managers, and strategic professionals, who are driven to sharpen their strategic... more
Embark on a comprehensive journey into Embedded Systems with this course. Module 1, \"Introduction to Embedded Systems,\" lays the foundation by exploring principles, architectures, and essential... more
In this 2-hour long project-based course, you will be able to Create an AI assistant using OpenAI\'s playground UI, publish an AI application using Chipp.ai, and evaluate and refine your AI... more
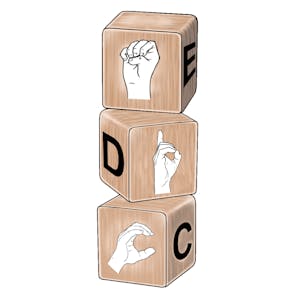
Many Deaf children around the world still leave school functionally illiterate. In some cases, there is no allowance made for the education of Deaf children at all. This 4-week course provides you... more
It is during the shortlisting and interviewing processes, which are typically undertaken by a single panel, that candidates most often report being unfairly assessed during recruitment efforts. In... more